Questões de Concurso
Filtrar
180 Questões de concurso encontradas
Página 20 de 36
Questões por página:
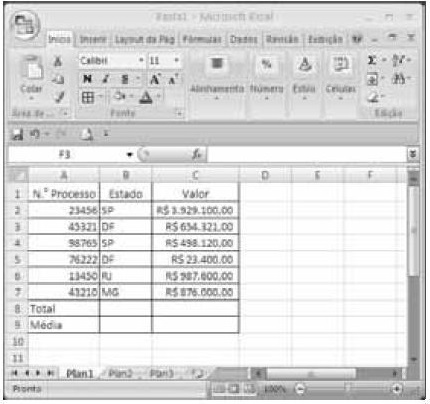
Para formatar a fonte dos valores abaixo de R$ 500.000,00 com a cor vermelha e a dos valores acima de R$ 500.000,00 com a cor azul, é suficiente selecionar a coluna, clicar o menu Fórmulas, digitar =SE(C2<500000;"vermelho";"azul") e arrastar tudo, copiando a fórmula para as demais células dessa coluna.
Para classificar os processos do menor valor para o maior, é suficiente selecionar as células de C2 até C7; clicar a ferramenta  ; selecionar a opção Classificar do Menor para o Maior e, em seguida, clicar o botão Classificar.
; selecionar a opção Classificar do Menor para o Maior e, em seguida, clicar o botão Classificar.
Ao serem selecionados os cabeçalhos apresentados na primeira linha da planilha em edição e se clicar a ferramenta  , os cabeçalhos serão automaticamente centralizados tanto horizontal quanto verticalmente.
, os cabeçalhos serão automaticamente centralizados tanto horizontal quanto verticalmente.
Para se obter o valor total desses processos, é suficiente clicar a célula C8; pressionar a ferramenta  e, em seguida, pressionar a tecla
e, em seguida, pressionar a tecla  .
.